LogRhythm tools tailor to the Kingdom of Saudi Arabia's Essential Cybersecurity Controls (ECC) - Cyber Risk Leaders

LogRhythm Launches Tools for Rapidly Adopting the Kingdom of Saudi Arabia's Essential Cybersecurity Controls (ECC) | LogRhythm
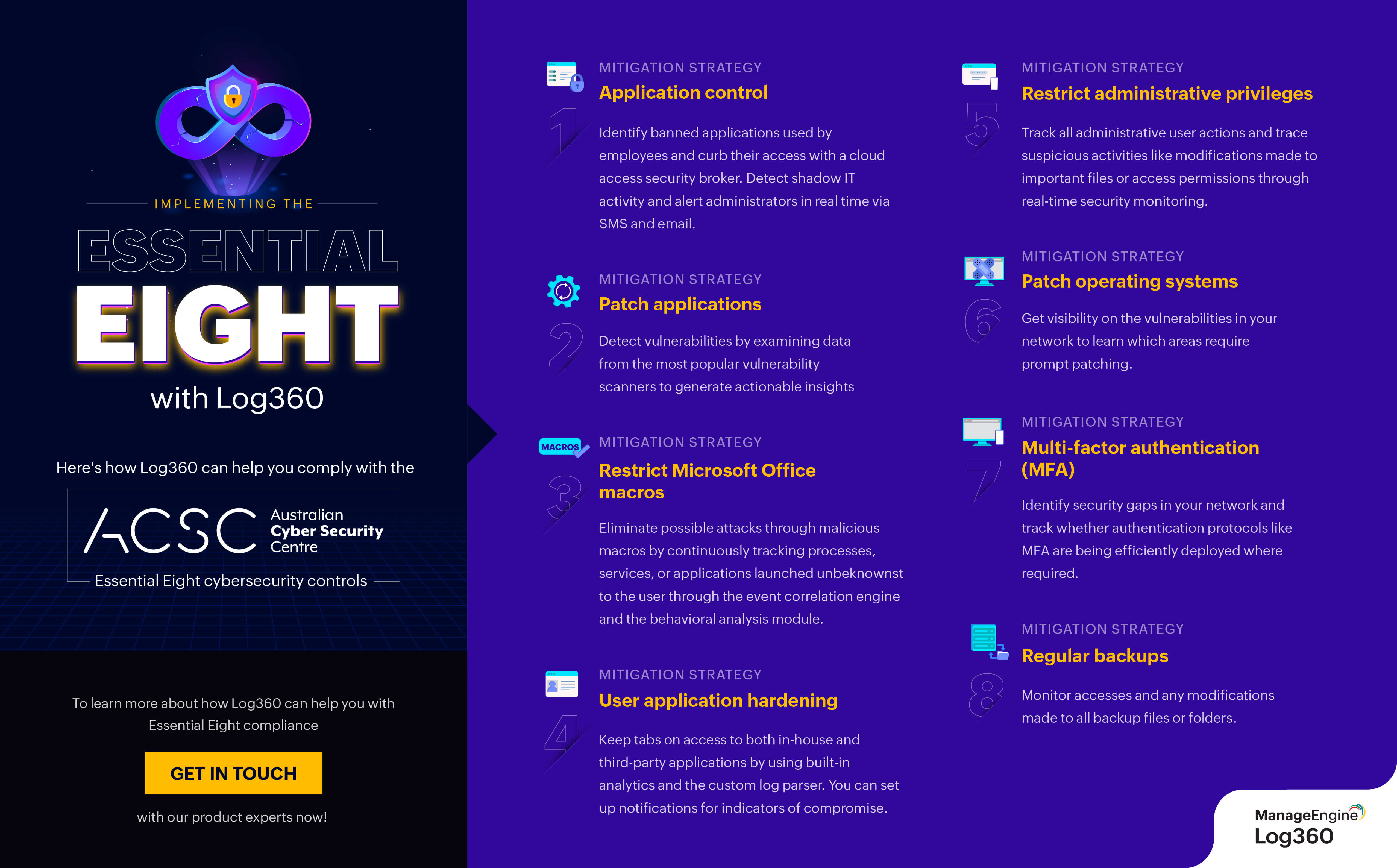
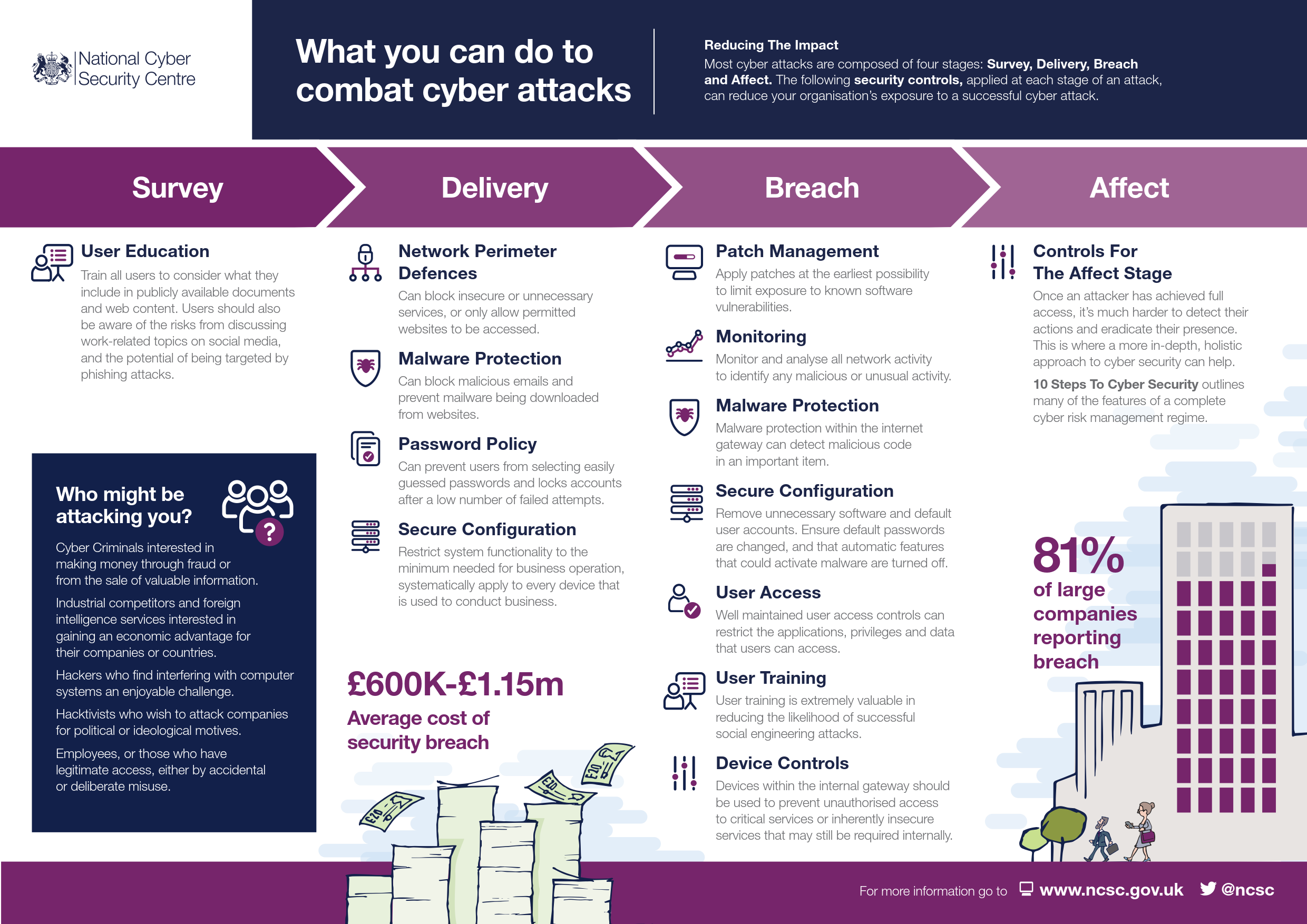
Essential Eight explained: ACSC's key security controls for organizational cybersecurity | Data Security